CMMC 2.0 is the updated cybersecurity framework from the Department of Defense (DoD), designed to protect sensitive information within the Defense Industrial Base (DIB). It simplifies compliance by reducing certification levels from five to three and aligning closely with existing standards like NIST SP 800-171. Here’s what you need to know:
-
3 Certification Levels:
- Level 1: For handling Federal Contract Information (FCI); requires 15 practices and allows self-assessments.
- Level 2: For Controlled Unclassified Information (CUI); requires 110 practices and aligns with NIST SP 800-171.
- Level 3: For highly sensitive information; adds 24 practices from NIST SP 800-172.
-
Key Changes:
- Simplified structure and reduced certification levels.
- Elimination of unique CMMC 1.0 requirements.
- Self-assessment allowed for Level 1 and some Level 2 organizations.
- Clearer guidelines and tools for compliance.
-
Timeline:
- 2025: Transition phase begins with CMMC requirements in select contracts.
- 2026: More contracts include CMMC requirements; preparation becomes critical.
- 2027-2028: Full implementation across the DIB, with mandatory third-party assessments for many Level 2 organizations.
To prepare for 2026, organizations should:
- Conduct a gap analysis to identify areas needing improvement.
- Develop detailed System Security Plans (SSPs) and policies.
- Implement continuous monitoring for real-time security oversight.
- Train staff to reduce human error and strengthen security practices.
CMMC 2.0 emphasizes preparation and ongoing compliance. Early action can help organizations meet deadlines, secure contracts, and maintain a strong cybersecurity posture.
CMMC 2.0 Framework Structure and Changes from Version 1.0
CMMC 2.0 takes a more streamlined approach to cybersecurity compliance, simplifying its structure to make it easier for organizations to meet requirements. One of the most noticeable changes is the reduction of certification levels from five to three, creating a clearer and more accessible framework for businesses to follow.
This updated version builds on established standards, particularly NIST SP 800-171, focusing on practical, real-world implementation rather than theoretical compliance.
3 Certification Levels in CMMC 2.0
CMMC 2.0 introduces a three-level certification system, tailored to match the sensitivity of the information organizations handle and the contracts they pursue:
- Level 1 (Foundational): This level applies to organizations managing Federal Contract Information (FCI). It includes 15 security practices, and most organizations can complete self-assessments, making this the most straightforward tier.
- Level 2 (Advanced): Aimed at organizations handling Controlled Unclassified Information (CUI), this level requires compliance with 110 security practices, aligning closely with the NIST SP 800-171 framework.
- Level 3 (Expert): Designed for those managing highly sensitive unclassified information, Level 3 builds on Level 2 by adding 24 more security practices from NIST SP 800-172, for a total of 134 practices.
"The Department of Defense (DoD) will indicate the necessary CMMC level in the solicitation and in any Requests for Information (RFIs) if utilized."
- Office of the Under Secretary of Acquisition and Sustainment (OUS A&S)
This tiered system reflects the overall goal of simplifying compliance while addressing varying levels of security needs.
Simplified Processes and Reduced Requirements
One of the biggest shifts in CMMC 2.0 is the reduction of certification levels, which cuts down on confusion and removes redundant requirements from the original framework.
A major improvement is the removal of unique CMMC 1.0 requirements that didn’t align with existing standards. This change allows organizations already working on NIST compliance to use much of their existing groundwork, saving time and resources.
CMMC 2.0 also introduces greater flexibility. For example, Level 1 organizations can conduct self-assessments, while Level 2 organizations benefit from clearer guidelines and phased implementation. The elimination of Plans of Action and Milestones (POA&Ms) further simplifies the process.
To make compliance even more manageable, the Department of Defense (DoD) has provided tools like the Level 1 Self-Assessment Guide and the Level 2 Assessment Guide, offering organizations a clearer path to certification.
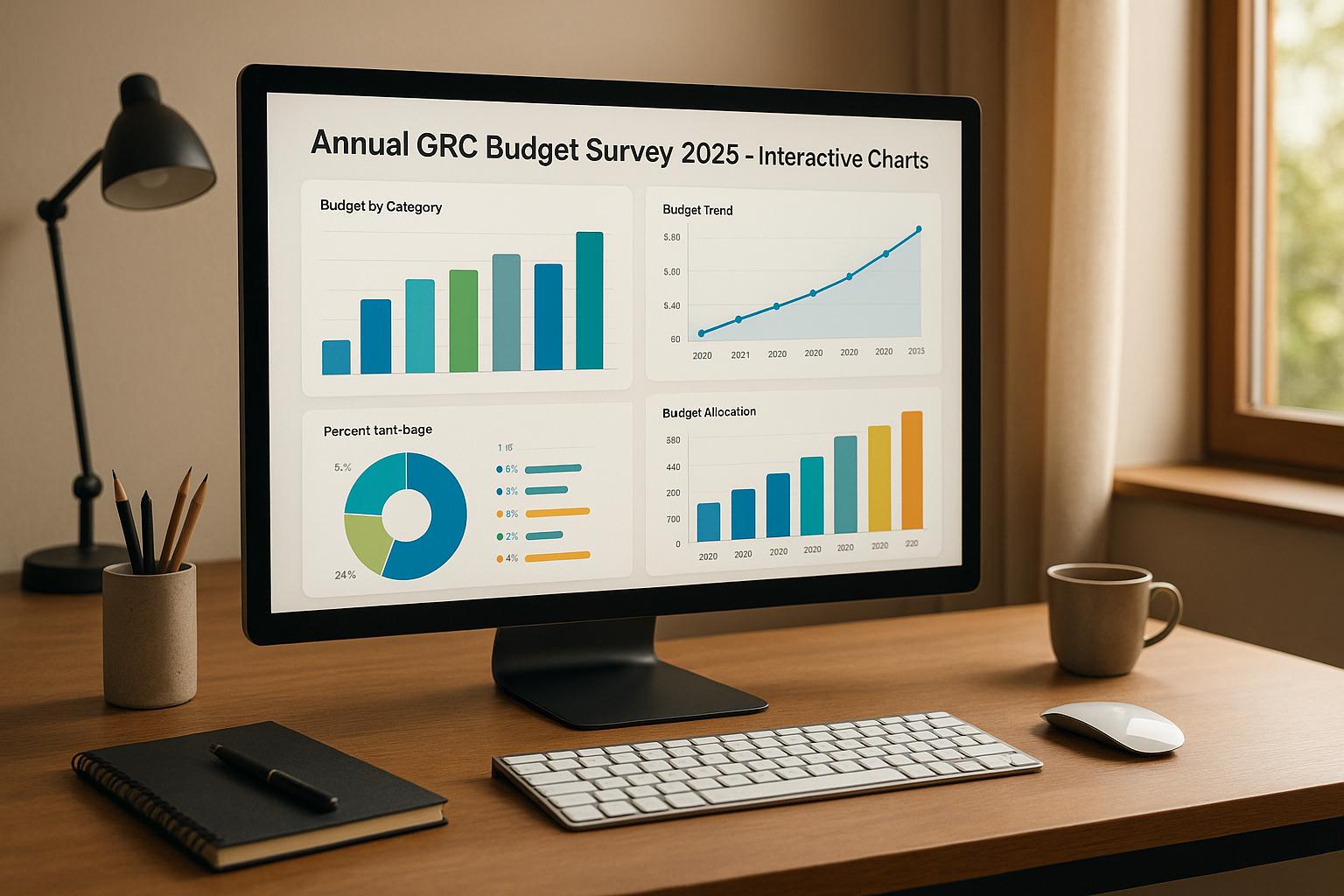
Important Dates and Compliance Deadlines
CMMC 2.0’s rollout includes a phased timeline, giving organizations time to prepare and adapt:
- 2025: The transition phase begins. During this time, the DoD will include CMMC requirements in select contract solicitations. Organizations should use this period to perform gap analyses and address any compliance issues, as preparation can take 6 to 12 months.
- 2026: The pace picks up with CMMC requirements appearing in more DoD contracts. Organizations that delay compliance efforts may find themselves unable to compete for new or renewed contracts.
- 2027–2028: By this stage, CMMC 2.0 will be fully implemented across the Defense Industrial Base. All applicable contracts will specify the required certification levels, and many Level 2 organizations will no longer have the option of self-assessments, requiring third-party evaluations instead.
This timeline underscores the importance of early preparation, especially for subcontractors. Since CMMC requirements will extend throughout the supply chain, prime contractors must ensure their subcontractors meet the appropriate certification levels. With a limited number of qualified assessors and the complexity of achieving compliance, starting early can provide a competitive edge.
How to Prepare for CMMC 2.0 Compliance by 2026
Getting ready for CMMC 2.0 compliance means evaluating your current security measures, documenting your processes, and implementing continuous monitoring. With the timeline moving quickly, these actions need to happen sooner rather than later. Following the streamlined structure of CMMC 2.0, here’s how you can meet the updated certification standards.
Running a Gap Analysis and Risk Assessment
One of the first steps in preparing for CMMC 2.0 is conducting a thorough gap analysis. This involves comparing your current security controls against the specific requirements of your target certification level - whether that’s Level 1, Level 2, or Level 3.
Start by taking stock of your existing security measures across all systems that handle Federal Contract Information (FCI) or Controlled Unclassified Information (CUI). Pay close attention to areas like access controls, encryption methods, and network security. If your organization has already worked toward NIST SP 800-171 compliance, you might find that many of your existing controls already align with CMMC 2.0 requirements.
Next, prioritize any gaps you identify. Consider factors like how complex the fix is, the associated costs, and how critical the system in question is. For example, implementing multi-factor authentication might be relatively straightforward, while setting up a robust continuous monitoring system could require significant time and resources.
Document your findings in a way that aligns with the CMMC 2.0 control families. This will help you track your progress and clearly communicate updates to stakeholders. Keep in mind that some security practices are interconnected - fixing one issue, like an access control gap, might require changes to related systems, such as identity management or audit logging.
Creating Required Documentation for Compliance
CMMC 2.0 compliance hinges on having detailed documentation that shows how your organization implements and maintains its security practices. At the center of this effort is the System Security Plan (SSP), which provides a comprehensive overview of your security controls and how they’re applied.
Your SSP should clearly outline system boundaries, data flows, how controls are implemented, and who is responsible for them. Avoid relying on generic templates - your documentation should accurately reflect your organization’s specific environment.
In addition to the SSP, you’ll need well-defined policies and procedures. These documents provide clear instructions and assign accountability. For instance, an incident response policy should detail who to notify during a security event, what tools to use in investigations, and how to document findings.
It’s also important to establish procedures for collecting evidence of compliance. Identify what evidence is needed to demonstrate adherence to each security practice and assign responsibility for maintaining it. Automated tools can make this process easier by capturing the required information in the correct format, reducing manual effort. Once your documentation is complete, ongoing monitoring will help ensure your compliance remains intact.
Setting Up Ongoing Monitoring and Reporting
Continuous monitoring shifts the focus from periodic compliance reviews to real-time oversight of security controls. For organizations pursuing CMMC Level 2, Control 3.12.3 requires ongoing assessment to confirm that security measures remain effective. This approach not only improves visibility into your security posture but also allows for faster detection and response to vulnerabilities or incidents. It also supports better risk management through accessible dashboards and reporting.
Automation plays a key role here. Automated systems can keep hardware, software, and firmware inventories up to date while ensuring that monitoring outputs are specific, measurable, actionable, relevant, and timely (SMART). For those aiming for Level 3, continuous monitoring should include tracking metrics like incident response times, system uptime, and overall performance. Ultimately, achieving and maintaining CMMC 2.0 compliance means embedding security into your daily operations rather than treating it as a one-time task.
How Cycore Makes CMMC 2.0 Compliance Easier
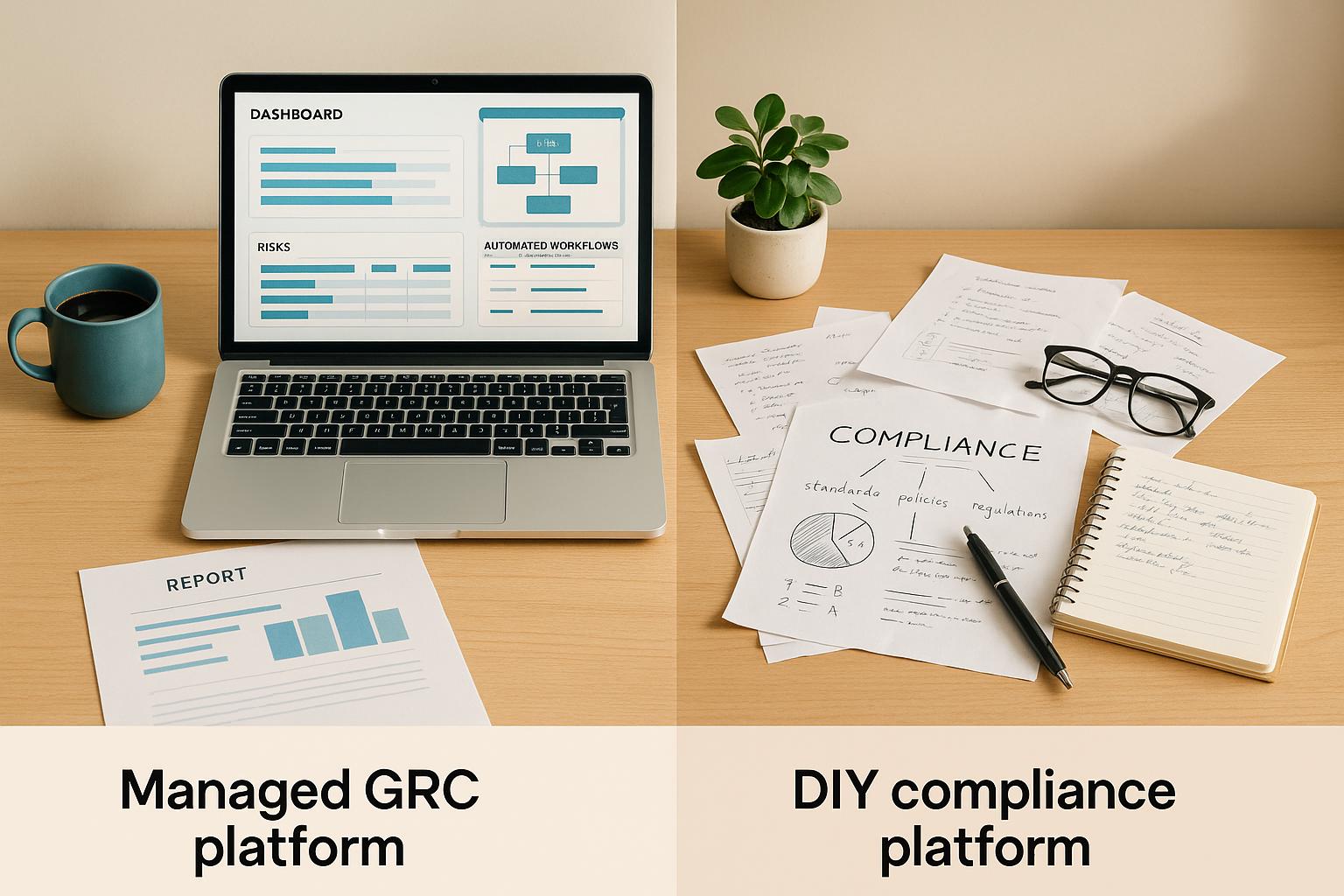
Navigating the path to CMMC 2.0 compliance doesn’t have to overwhelm your resources or pull your team away from critical product development. Cycore steps in as your fractional security, compliance, and privacy team, managing the entire compliance process so you can focus on growing your business and meeting the 2026 deadlines without disruption.
Unlike traditional GRC tools that simply track tasks, Cycore takes a hands-on approach. Instead of handing you a checklist, we integrate with your team to design and implement a security program specifically tailored to meet your CMMC 2.0 requirements. Here’s how our approach simplifies every stage of the compliance process.
Comprehensive Compliance Management
Cycore handles every step of your CMMC 2.0 journey, from the initial assessment to ongoing maintenance. We start with a detailed gap analysis to evaluate your current security posture against the requirements of your target certification level - whether it’s Level 1, Level 2, or Level 3.
Our team creates customized documentation, including your System Security Plan (SSP) and policies, ensuring they reflect your specific environment. These documents include everything from system boundaries and data flows to control implementations and clearly assigned responsibilities.
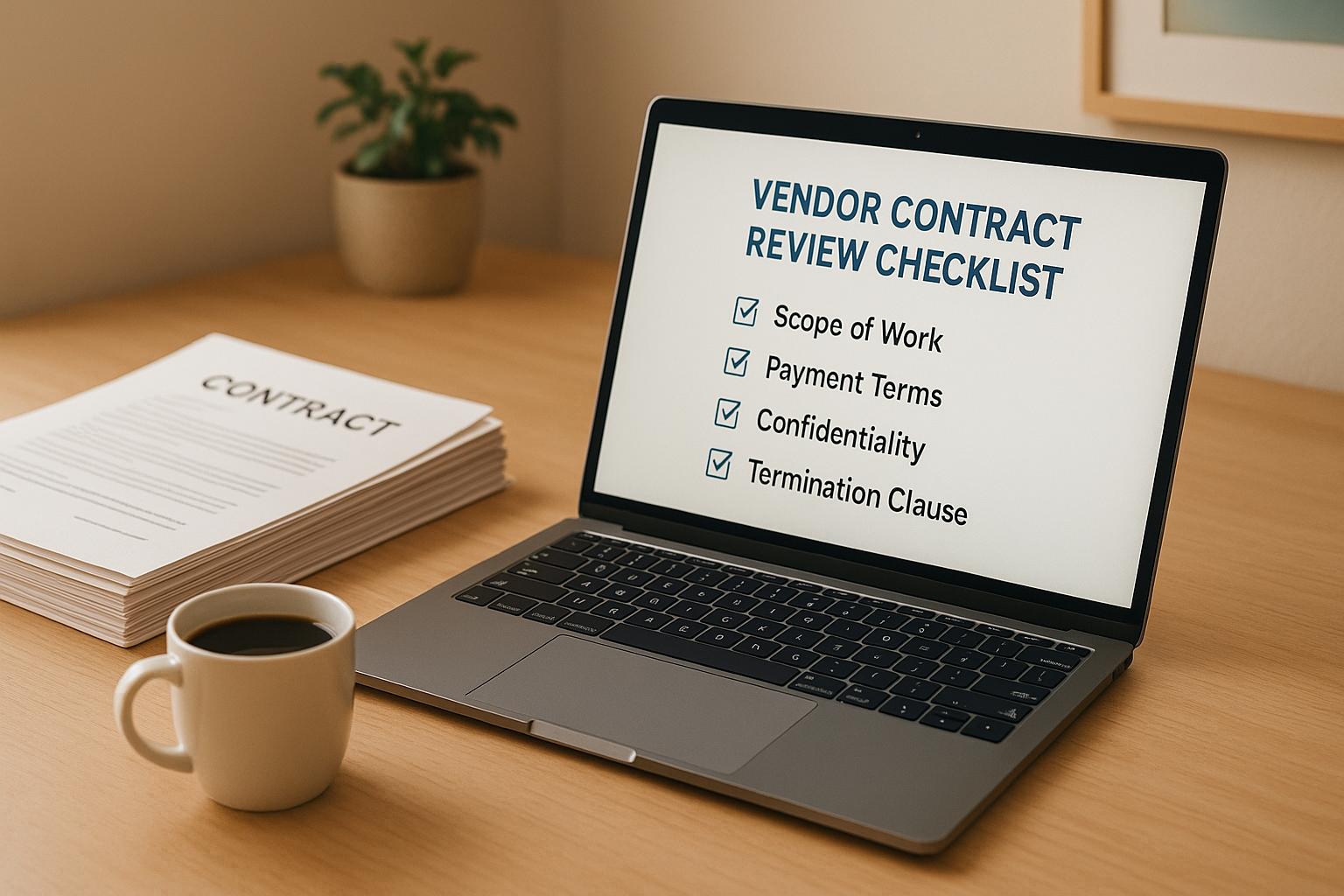
We also manage the implementation of critical controls and oversee evidence collection to ensure audit readiness. For organizations managing Federal Contract Information (FCI) or Controlled Unclassified Information (CUI), we align your security measures with CMMC 2.0 standards. Additionally, we take care of vendor due diligence, helping you assess third-party security practices and establish proper agreements.
Combining AI Tools with Expert Guidance
Our hybrid approach blends cutting-edge AI tools with the expertise of seasoned consultants to make compliance faster and more efficient. AI-driven automation continuously collects evidence, identifies gaps, and streamlines processes, reducing errors and saving costs.
At the same time, our subject matter experts focus on the strategic side of compliance, ensuring that the AI’s work aligns with your business goals. These experts provide critical guidance for risk management, control prioritization, and resource allocation, helping you make informed decisions.
While your internal team stays focused on delivering products and serving customers, we handle the complexities of CMMC 2.0 compliance. Whether you use tools like Vanta, Drata, or Secureframe, we integrate seamlessly with your existing systems. We also work across your technology stack, including platforms like Jira, Asana, Okta, Azure AD, AWS, GCP, and Azure.
Why Partnering with Cycore Makes Sense
Beyond simplifying compliance, Cycore delivers tangible business benefits. One immediate advantage is faster deal closure. When customers request security certifications or send questionnaires, we respond quickly with the necessary documentation and even join customer calls to address compliance concerns, helping you clear sales roadblocks and close contracts faster.
Our managed service model is also cost-effective. Instead of hiring a full-time compliance team, you gain access to a fractional CISO-level lead and a team of specialists for a predictable monthly fee. This eliminates the costs and challenges of recruiting, training, and retaining in-house compliance experts.
Another key benefit is staying audit-ready year-round. With continuous monitoring and evidence collection, you avoid the last-minute scramble that often precedes audits or security reviews. Whether it’s an audit, a customer inquiry, or a regulatory check, you’ll always be prepared.
By taking the burden of compliance off your shoulders, we help your engineering and operations teams stay focused on building and selling. This often leads to improved productivity, faster product development, and a boost in team morale.
Our process begins with a structured onboarding phase, including discovery, gap analysis, and roadmap creation. From there, we transition into ongoing operations, adapting as your compliance needs evolve to ensure you always meet the latest CMMC 2.0 requirements.
sbb-itb-ec1727d
Maintaining CMMC 2.0 Compliance Over Time
Getting your CMMC 2.0 certification is just the start - keeping it is where the real challenge begins. As your organization grows and changes, staying compliant becomes an ongoing effort. With around 80,000 companies handling Controlled Unclassified Information (CUI) required to meet all 110 NIST 800-171 controls at CMMC Level 2 to qualify for Department of Defense (DoD) contracts, maintaining compliance isn't just important - it's a business necessity.
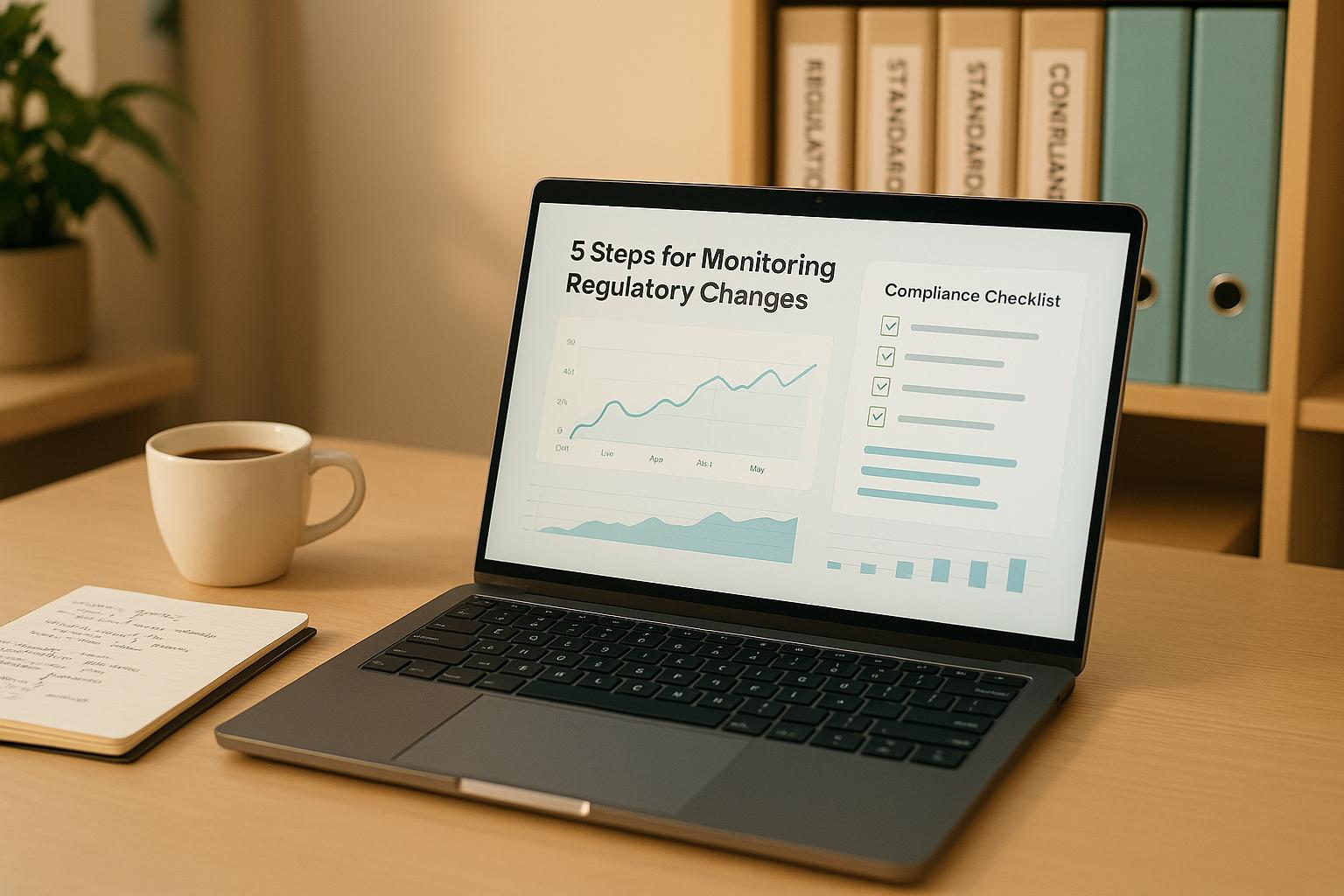
The move from one-time compliance checks to continuous monitoring marks a shift in how organizations handle cybersecurity. CMMC 2.0 demands constant attention, making it essential to adopt long-term strategies. These strategies ensure your compliance efforts remain effective, adaptable, and ready for audits at any time.
Managing Audit Preparation More Effectively
For many teams, audit preparation can feel like a fire drill - rushing to gather evidence and update documentation at the last minute. This reactive approach increases the risk of overlooking compliance gaps.
The smarter way? Continuous evidence collection. Instead of scrambling, organizations that keep their documentation audit-ready throughout the year can respond to regulatory inquiries in days rather than weeks. This involves automating processes like log collection, vulnerability scans, and ticket tracking, all tied directly to specific control families.
Regular internal reviews, such as quarterly audits, add another layer of assurance. These check-ins confirm that your processes are working as intended and that any Plan-of-Action items are on track. By addressing potential issues early, you can avoid surprises during formal audits.
Centralizing your evidence makes it easier to share with auditors, customers, or other stakeholders. This streamlined approach saves time and reduces stress when audit season rolls around.
Using Automation for Repetitive Compliance Tasks
Relying on manual processes for compliance isn’t sustainable, especially since 95% of breaches are caused by human error.
Automation offers a scalable solution. It can handle repetitive tasks like control testing, provide real-time insights, and minimize errors, freeing up your team for higher-value work. By continuously monitoring your systems, automation ensures that security gaps are addressed immediately rather than during an audit months later.
When choosing automation tools, look for solutions that offer at least 90% connector coverage with your existing systems. The best platforms integrate seamlessly with tools like Jira, Asana, Okta, Azure AD, AWS, GCP, and Azure.
Before rolling out automation, review your workflows to identify areas where it can make the biggest difference. Focus on tasks like policy updates, technical control testing, and risk assessments. Once implemented, track the results - measure time savings, improved accuracy, and the reduction of manual tasks. This data will help you refine your processes and build a proactive compliance program aligned with the CMMC 2.0 framework.
Training Staff and Building Security Awareness
Even with advanced automation, your workforce remains a critical part of your security strategy. Human error plays a role in 82% of breaches. Just as continuous monitoring strengthens technical defenses, ongoing training reinforces the human side of compliance. That’s why the CMMC 2.0 Awareness and Training (AT) domain is so important for long-term success.
CMMC 2.0 Level 2 requires a structured cybersecurity training program aligned with NIST SP 800-171 standards. This isn’t just about meeting a requirement - effective training reduces mistakes, strengthens your security culture, and helps prevent insider threats.
The AT domain includes three critical controls: Role-Based Risk Awareness (AT.L2-3.2.1), Role-Based Training (AT.L2-3.2.2), and Insider Threat Awareness (AT.L2-3.2.3). Each of these requires proper documentation and evidence to demonstrate their effectiveness.
Building a security-first mindset takes more than an annual training session. It requires leadership support, regular updates, and fostering a sense of accountability among employees. This approach is especially important given that 97% of organizations face email-based phishing attacks, and 80% of professionals believe their companies are at risk due to accidental data leaks.
Frequent updates keep security awareness relevant. Instead of relying on once-a-year sessions, implement monthly security tips, quarterly phishing simulations, and immediate follow-up training for employees who fall for simulated attacks. This ongoing effort makes security awareness part of everyday work, not just an annual checkbox.
Investing in thorough training programs pays off. Organizations with strong security awareness programs experience fewer incidents, respond faster to threats, and maintain a stronger overall security posture. When employees understand their role in safeguarding sensitive information like CUI, they become active defenders of your security program rather than potential vulnerabilities.
Key Points for CMMC 2.0 Compliance Success
CMMC 2.0 reshapes the cybersecurity landscape for defense contractors and their supply chain partners, making early preparation essential for staying ahead. A solid strategy built on these principles can guide organizations toward compliance while minimizing disruptions.
The framework's three-tier certification structure simplifies the process by tailoring requirements to match an organization's risk level and the sensitivity of the data it handles. Conducting early gap analyses, implementing necessary controls, and maintaining thorough documentation are critical steps to ensure readiness for audits, as self-attestation transitions to third-party evaluations.
Consistently collecting evidence and using automated monitoring tools ensures organizations remain prepared for audits. This proactive approach minimizes last-minute stress and demonstrates a strong security posture. Automation also helps by handling repetitive tasks, reducing the risk of human error, and freeing up team members to focus on more strategic priorities.
Cultivating ongoing security awareness and collaborating with a compliance-focused partner, such as Cycore, can turn the often daunting compliance process into a strategic advantage. This allows internal teams to dedicate more energy to core business objectives while staying on track with CMMC 2.0 requirements.
FAQs
What are the key differences between CMMC 1.0 and CMMC 2.0, and how do they affect organizations already following NIST standards?
CMMC 2.0 has made things simpler by cutting the certification levels from five down to three. One of the standout updates is that Level 2 now directly aligns with NIST SP 800-171. This change makes it easier for many organizations to understand and meet the necessary requirements.
If your business is already following NIST standards, you're likely in a good spot to tackle CMMC 2.0 Level 2. That said, you'll still need to double-check that your compliance documentation and practices line up with the updated CMMC 2.0 guidelines. Starting preparations early and staying on top of the changes will make the transition much smoother.
What steps should organizations take to prepare for CMMC 2.0 by 2026, and how can early preparation benefit them?
To gear up for CMMC 2.0 by 2026, start with a thorough readiness assessment. This step helps pinpoint compliance gaps and highlights areas needing improvement. Pay close attention to critical elements like multi-factor authentication, access controls, and strengthening governance and documentation processes. Using compliance automation tools and seeking guidance from certified CMMC consultants can make the journey smoother and more efficient.
Starting early comes with big benefits. It not only secures your place for assessments but also helps position your business as a preferred supplier in the defense sector. Plus, it gives you a competitive edge to win more contracts. By planning ahead, you’ll be well-prepared to handle both short-term and long-term compliance requirements.
What does the tiered certification system in CMMC 2.0 mean for subcontractors in the Defense Industrial Base, and what challenges might they face in meeting compliance requirements?
The CMMC 2.0 tiered certification system requires subcontractors within the Defense Industrial Base (DIB) to achieve specific certification levels based on the sensitivity of the information they manage. These levels are designed to ensure that subcontractors adhere to cybersecurity standards necessary for safeguarding controlled unclassified information (CUI) and federal contract information (FCI).
Subcontractors face several challenges in meeting these requirements. These include adjusting internal processes to align with CMMC standards, upgrading technology to meet security benchmarks, and handling the administrative burden of documentation and audits. Additionally, maintaining consistent compliance across all operations is critical to avoiding risks to contract eligibility. Starting preparations early and taking a proactive approach can make navigating these requirements more manageable.