CMMC 2.0 simplifies cybersecurity compliance for defense contractors by reducing five levels to three: Level 1 (basic controls for FCI), Level 2 (advanced controls for CUI), and Level 3 (strict controls for high-risk CUI). Certification is mandatory for companies wanting to secure DoD contracts. Here's what you need to know:
Compliance ensures eligibility for DoD contracts while protecting sensitive data. Follow the checklist for a structured approach to meet and maintain certification requirements.
CMMC 2.0 Levels and Key Changes
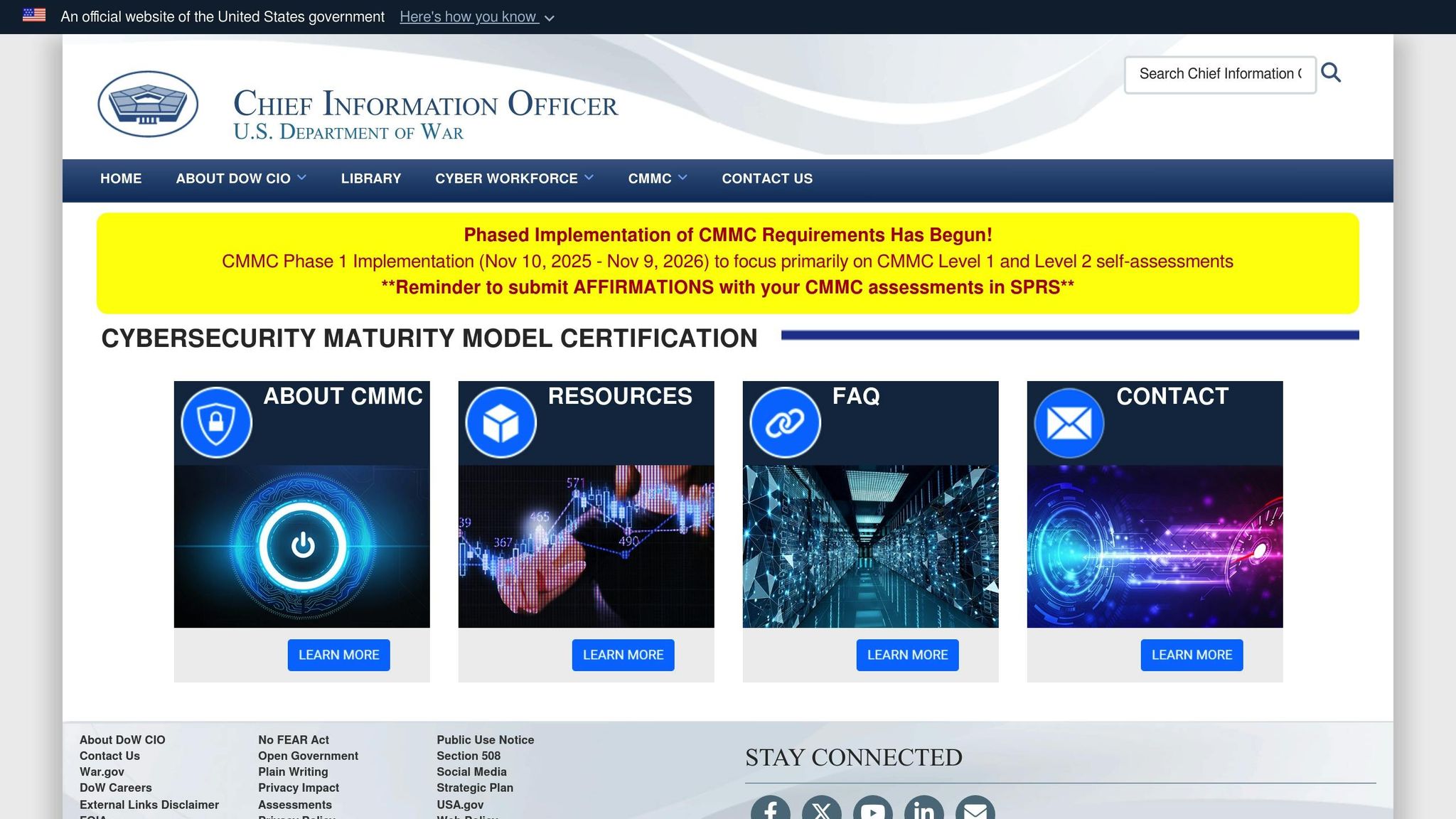
The Cybersecurity Maturity Model Certification (CMMC) framework underwent significant updates with the introduction of CMMC 2.0. Announced on July 17, 2021, the revised framework simplifies the original five-tier system into three levels: Foundational (Level 1), Advanced (Level 2), and Expert (Level 3). The final rule officially took effect on December 16, 2024. Unlike its predecessor, CMMC 2.0 emphasizes ongoing management and enforcement of cybersecurity controls rather than relying solely on one-time assessments. These changes aim to streamline both the assessment and compliance processes.
One major improvement is increased flexibility in assessments. Previously, all levels required third-party evaluations, but under CMMC 2.0, Level 1 and certain Level 2 contracts now allow for self-assessments. Additionally, organizations can use Plans of Action and Milestones (POA&Ms) to address non-critical control gaps, granting up to 180 days for remediation. It's important to note that each level builds on the one before it, meaning compliance with lower-level requirements is mandatory for higher-level certifications.
Here’s a quick breakdown of the updated levels:
CMMC Level
Data Protected
Requirements
Assessment Process
POA&Ms Allowed
Federal Contract Information (FCI)
17 practices aligned with
Annual self-assessment with annual affirmation
Not permitted
Controlled Unclassified Information (CUI)
110 practices aligned with NIST SP 800-171 Rev. 2
Third-party assessment every 3 years for prioritized CUI, or self-assessment for non-prioritized CUI with annual affirmation
Permitted; deficiencies must be resolved within 180 days
Highly sensitive CUI on critical DoD programs
110 NIST SP 800-171 practices plus 24 controls from NIST SP 800-172
Government-led assessment every 3 years with annual affirmation
Permitted, with stricter limitations
Level 1: Basic Requirements
Level 1 is designed to protect Federal Contract Information (FCI) by implementing 17 safeguarding practices aligned with FAR 52.204-21. Contractors handling non-public government data at this level can conduct annual self-assessments. However, POA&Ms are not allowed for addressing deficiencies in this tier.
Level 2: Advanced Requirements
For handling Controlled Unclassified Information (CUI), Level 2 builds upon Level 1 by incorporating 110 cybersecurity practices from NIST SP 800-171 Rev. 2. The type of assessment required depends on the contract:
POA&Ms are permitted at this level but only for non-critical deficiencies, which must be resolved within 180 days.
Level 3: Expert Requirements
Level 3 is the most stringent, addressing high-risk scenarios that involve highly sensitive CUI in critical Department of Defense (DoD) programs. This level includes all 110 practices from NIST SP 800-171 and adds 24 advanced controls from NIST SP 800-172. Certification requires government-led assessments conducted by the Defense Industrial Base Cybersecurity Assessment Center (DIBCAC) every three years, along with annual affirmations. While POA&Ms are permitted, they come with stricter limitations compared to Level 2.
Complete CMMC 2.0 Implementation Checklist
Follow these steps to achieve CMMC 2.0 compliance, covering both technical and administrative controls.
Identify Your Required CMMC Level
The first step is determining which CMMC level applies to your organization based on the type of government data you handle. This will define your compliance requirements, assessment process, and timeline.
Check your contracts for specific language indicating the required level. Keep in mind that future contracts may demand a higher certification level. Refer to the official level descriptions for detailed requirements.
Perform a Gap Assessment
Assess your current security controls against CMMC requirements to identify gaps and plan remediation. This ensures your security posture aligns with compliance needs.
For Level 1, focus on these 10 key areas:
For Level 2, evaluate controls across all 14 NIST SP 800-171 domains. Pay extra attention to areas like multifactor authentication, audit logging, incident response, and encryption (both in transit and at rest) using FIPS 140-2 validated cryptographic modules.
Document each control as fully, partially, or not implemented. For partial implementation, note specific gaps and outline the steps needed to close them. If possible, consult cybersecurity experts familiar with CMMC to uncover any overlooked vulnerabilities.
Create Policies and Procedures
Develop comprehensive policies and procedures, including a System Security Plan (SSP), incident response plans, and configuration management policies. These documents should address the gaps identified during your assessment and support your technical controls. Assessors will scrutinize these policies during evaluations.
Set Up Technical Controls
Technical controls are critical for securing government information. Ensure these align with NIST requirements while maintaining operational efficiency.
Once these controls are in place, document them thoroughly for assessment purposes.
Get Ready for Assessments
With policies and controls established, focus on preparing for assessments. This involves organizing documentation, gathering evidence, and validating processes to demonstrate compliance.
Train key personnel on the assessment process, including how to present evidence and respond to assessor questions. Practice interviews can help staff feel confident and prepared for formal evaluations.
How Cycore Simplifies CMMC 2.0 Compliance
Achieving CMMC 2.0 compliance can be a daunting task, especially when you consider the expertise, time, and resources it demands. Many organizations struggle to handle this internally, but Cycore steps in to fill the gap. Their outsourced services offer comprehensive support throughout the compliance process - from the initial assessment to achieving full compliance.
Let’s explore how Cycore makes compliance management easier at every stage.
Complete Compliance Management
Cycore takes the complexity out of managing CMMC 2.0 requirements. Their services are designed to help businesses meet not only CMMC 2.0 standards but other frameworks as well, ensuring audit-ready compliance every step of the way.
The process starts with a thorough assessment to pinpoint gaps in your current security setup. From there, Cycore helps implement the necessary controls and creates documentation tailored to meet assessor expectations. As your business evolves, their scalable solutions grow with you, ensuring your compliance strategy remains effective over time.
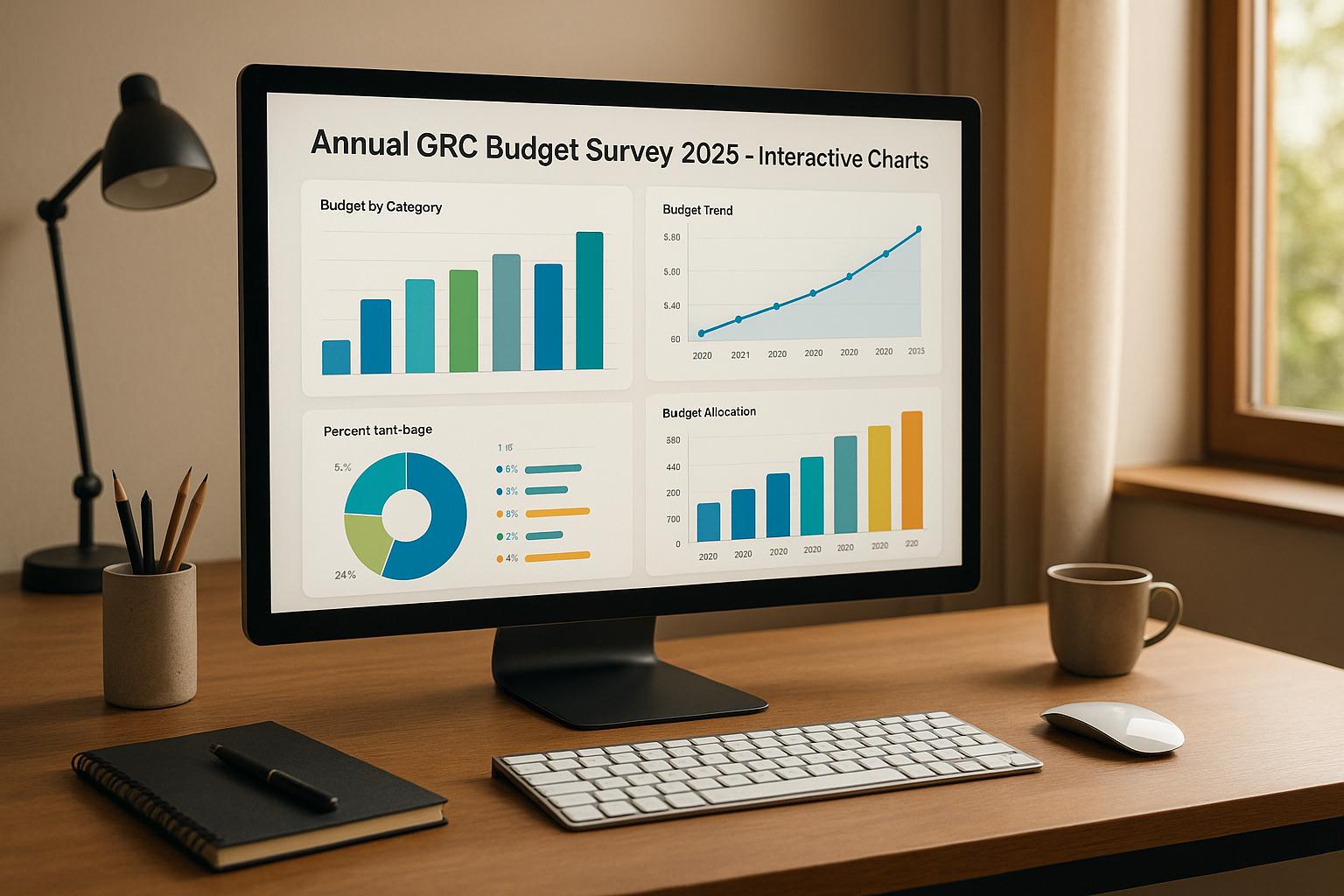
Virtual CISO & GRC Tool Administration
For organizations that need expert security guidance without committing to a full-time hire, Cycore's Virtual CISO (vCISO) service is an ideal solution. The vCISO works closely with your team to develop strong security strategies and oversee the implementation of required CMMC controls.
Cycore also offers GRC (Governance, Risk, and Compliance) Tool Administration services, which simplify the use of leading compliance platforms like Drata, Vanta, Secureframe, and Thoropass. These tools are configured to automate monitoring and streamline evidence collection. A great example of this in action is ReadMe, which used Cycore’s GRC Admin Services to significantly cut down on manual work. They reduced security questionnaire response times by 66%, saving an impressive 1,656 hours annually. Together, the vCISO and GRC services provide both strategic oversight and practical, day-to-day compliance support.
Continuous Support for Long-Term Compliance
Staying compliant with CMMC 2.0 is not a one-time effort - it requires ongoing attention. Cycore offers continuous support to ensure your organization remains prepared for audits and assessments. Their audit assistance ensures your documentation is well-organized and your team is ready for both self-assessments and third-party evaluations.
With flexible engagement options, you can choose the level of support that fits your needs. Whether you need help with initial implementation or ongoing management, Cycore’s services are designed to adapt. Regular reporting keeps leadership informed about compliance progress and upcoming requirements, enabling proactive planning to address potential risks efficiently.
sbb-itb-ec1727d
Maintaining Compliance and Audit Preparation
Once you’ve established solid controls and procedures, the next step is ensuring they remain effective over time. This means committing to continuous monitoring and staying ready for audits to maintain compliance.
CMMC 2.0 certification isn’t the finish line - it’s the starting point. Long-term compliance requires ongoing attention, including regular updates to security controls and refining how you handle incidents.
Continuous Monitoring and Updates
Compliance isn’t a “set it and forget it” process. Your security measures need to keep pace with evolving threats and changes in your business operations. One way to stay ahead is by using automated tools that monitor security controls, provide detailed logs, and send alerts for potential issues.
For organizations aiming for CMMC 2.0 Level 2 or Level 3, having a strong incident response plan is non-negotiable. This plan should align with NIST SP 800-171 standards and clearly define how to detect, respond to, and recover from cybersecurity incidents. Specifically, Level 2 compliance requires detailed steps for incident detection, response, recovery, and frequent testing of these measures. It also includes procedures for tracking and reporting incidents to ensure accountability.
With continuous monitoring systems and a well-tested incident response plan in place, your next focus should be audit readiness.
Audit Preparation Best Practices
Getting ready for an audit means putting your incident response efforts under the microscope. Make sure your incident response playbooks are up-to-date and that your team is fully trained to execute them effectively. For Level 2 compliance, you’ll also need clear processes for tracking and reporting incidents, including meeting Department of Defense (DoD) reporting requirements.
To streamline the audit process, integrate continuous monitoring and incident response activities into your team’s daily workflow. This not only keeps you prepared but also ensures compliance becomes a natural part of your operations.
Key Takeaways
Achieving compliance with CMMC 2.0 requires a focused, results-oriented strategy. The framework is divided into three levels - Basic, Advanced, and Expert - each with its own set of controls and documentation tailored to your organization's role in the defense supply chain.
Step One: Determine your CMMC level early. This decision shapes the technical controls and documentation you'll need. Here's a quick breakdown:
Conduct a gap assessment to identify weaknesses in your current setup. Without this step, you risk wasting resources on unnecessary controls. The assessment should address both technical measures and administrative processes.
Make sure to document policies and procedures thoroughly. A current and well-prepared incident response plan is essential - not just for passing assessments, but also for maintaining ongoing compliance through continuous monitoring.
FAQs
What are the main differences between CMMC 1.0 and CMMC 2.0, and how do they affect defense contractors?
CMMC 2.0 condenses the original five-level framework into three distinct tiers: Level 1 (Foundational), Level 2 (Advanced), and Level 3 (Expert). This updated structure simplifies the certification process while upholding strong cybersecurity standards.
This streamlined approach helps contractors better understand and implement the necessary controls. It's crucial for defense contractors to identify the appropriate level based on the sensitivity of the data they manage and ensure compliance to maintain eligibility for Department of Defense contracts.
How can a company determine the right CMMC 2.0 level for compliance, and what steps should they take to figure this out?
To figure out the right CMMC 2.0 level for your organization, start by evaluating the types of Controlled Unclassified Information (CUI) you manage and how sensitive that data is. Then, take a close look at your current cybersecurity practices to see how they measure up against CMMC requirements. Lastly, review the specifics of your Department of Defense (DoD) contract, as it will clearly state the CMMC level required for compliance.
You’ll also want to factor in the size and complexity of your organization, as these can play a role in determining the certification level needed. By carefully analyzing these aspects, you’ll be better equipped to identify the appropriate CMMC 2.0 level and prepare for the steps needed to meet compliance standards.
What are the pros and cons of using self-assessments versus third-party assessments for CMMC 2.0 compliance?
For CMMC 2.0 compliance, the type of assessment your organization needs depends on your certification level and the kind of information you handle.
By understanding these assessment types, you can determine the most suitable path for your organization’s compliance needs.
Related Blog Posts
- Common Control Frameworks for Multi-Compliance
- What Is Compliance Mapping?
- NERC CIP Audit Preparation: 6 Steps
- Risk Assessment Steps for Regulatory Changes
{"@context":"https://schema.org","@type":"FAQPage","mainEntity":[{"@type":"Question","name":"What are the main differences between CMMC 1.0 and CMMC 2.0, and how do they affect defense contractors?","acceptedAnswer":{"@type":"Answer","text":"<p>CMMC 2.0 condenses the original five-level framework into three distinct tiers: <strong>Level 1 (Foundational)</strong>, <strong>Level 2 (Advanced)</strong>, and <strong>Level 3 (Expert)</strong>. This updated structure simplifies the certification process while upholding strong cybersecurity standards.</p> <ul> <li><strong>Level 1</strong> covers 17 essential cyber hygiene practices, focusing on basic safeguards.</li> <li><strong>Level 2</strong> incorporates the 110 security requirements outlined in <em>NIST SP 800-171</em>, ensuring more advanced protections.</li> </ul> <p>This streamlined approach helps contractors better understand and implement the necessary controls. It's crucial for defense contractors to identify the appropriate level based on the sensitivity of the data they manage and ensure compliance to maintain eligibility for Department of Defense contracts.</p>"}},{"@type":"Question","name":"How can a company determine the right CMMC 2.0 level for compliance, and what steps should they take to figure this out?","acceptedAnswer":{"@type":"Answer","text":"<p>To figure out the right <strong>CMMC 2.0 level</strong> for your organization, start by evaluating the types of <strong>Controlled Unclassified Information (CUI)</strong> you manage and how sensitive that data is. Then, take a close look at your current cybersecurity practices to see how they measure up against CMMC requirements. Lastly, review the specifics of your <strong>Department of Defense (DoD)</strong> contract, as it will clearly state the CMMC level required for compliance.</p> <p>You’ll also want to factor in the size and complexity of your organization, as these can play a role in determining the certification level needed. By carefully analyzing these aspects, you’ll be better equipped to identify the appropriate CMMC 2.0 level and prepare for the steps needed to meet compliance standards.</p>"}},{"@type":"Question","name":"What are the pros and cons of using self-assessments versus third-party assessments for CMMC 2.0 compliance?","acceptedAnswer":{"@type":"Answer","text":"<p>For <strong>CMMC 2.0 compliance</strong>, the type of assessment your organization needs depends on your certification level and the kind of information you handle.</p> <ul> <li> <strong>Level 1</strong>: This level allows for annual self-assessments. It’s often a more budget-friendly and flexible option for smaller businesses. However, it demands internal expertise and a solid grasp of compliance requirements to ensure everything is done correctly. </li> <li> <strong>Level 2</strong>: Here, the assessment type varies. Depending on the sensitivity of the controlled unclassified information (CUI) your organization manages, you might need either self-assessments or third-party assessments. Third-party assessments are typically more thorough and add credibility during audits but can be costlier and require more time. </li> <li> <strong>Level 3</strong>: This level involves government-led assessments conducted every three years. These assessments are the most rigorous, offering the highest level of scrutiny. While they provide comprehensive validation, they also demand extensive preparation and resources. </li> </ul> <p>By understanding these assessment types, you can determine the most suitable path for your organization’s compliance needs.</p>"}}]}